Identity misuse is emerging as one of the most underestimated risks in modern cybersecurity. In today’s environments, access is no longer limited to human users. Service accounts, API integrations, automation scripts and AI assistants authenticate directly against business-critical systems. They retrieve data, trigger workflows and execute transactions, using legitimate credentials and approved access paths.
When one of these identities is abused or compromised, nothing appears broken. The login is valid. The session is authenticated. The activity looks operational.
This is the core of identity misuse: legitimate access used in unintended or malicious ways. AI does not create this problem, but it accelerates it. As intelligent agents are granted broader autonomy and deeper integration, the number of non-human identities with real access continues to grow, and so does the potential impact of misuse.
So what does this shift mean for detection and response? And why do traditional monitoring models struggle to keep up? Let’s explore.
From compromise to abuse
Traditional security strategies are built around detecting compromise. Controls are designed to identify malware, exploitation attempts or suspicious authentication behavior. The assumption is simple: an attacker must bypass security mechanisms to gain access.Identity misuse breaks that assumption.
If access is already granted, no exploit is required. If credentials are valid, authentication does not raise alarms. If privileges are correctly assigned, activity falls within expected boundaries.
The attack surface shifts from technical vulnerabilities to trust relationships. Instead of breaking controls, attackers leverage legitimate identities that already have access to critical systems.
The expanding role of non-human identities
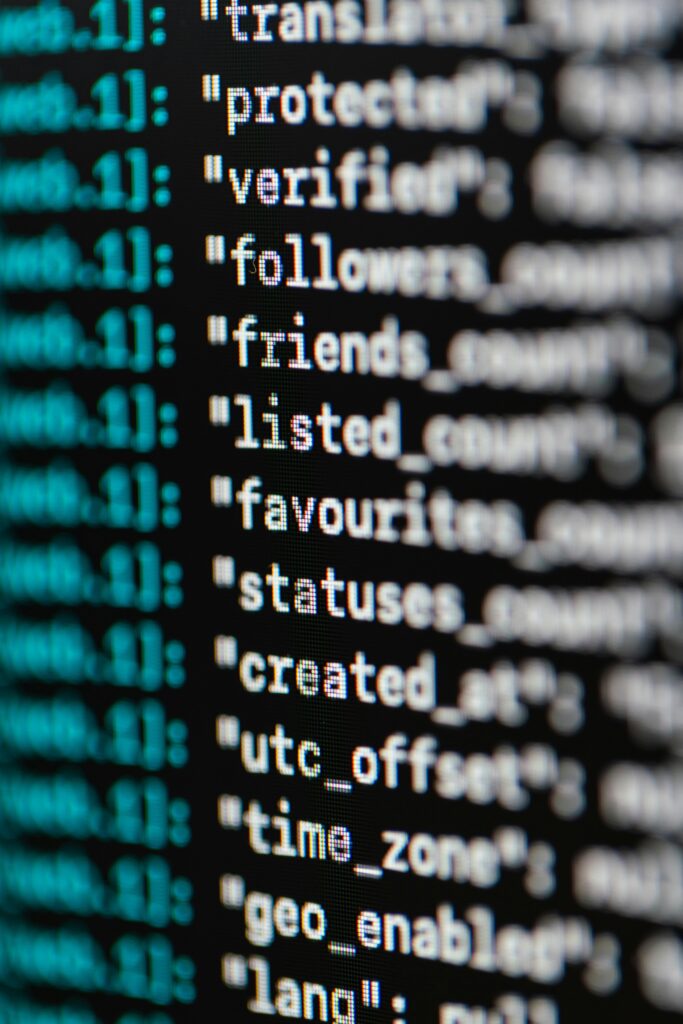
Modern environments depend on non-human identities to operate efficiently and at scale. Automation drives repetitive processes, integrations connect platforms, and AI assistants interact directly with applications and data layers. These identities are not peripheral; they are embedded in core business workflows.
Because they operate continuously, they are typically granted persistent access. As systems evolve, additional permissions are added to support new functionality. Over time, this leads to expanding privilege scopes, while ownership and oversight do not always evolve at the same pace. Access reviews tend to concentrate on human users, leaving automated identities comparatively less scrutinized.
AI agents further amplify this dynamic. They are intentionally designed to act autonomously within predefined boundaries, executing tasks without direct human intervention. As their functional capabilities grow, so does their operational importance, and with that, the level of access they require.
If such an identity is misused or compromised, the consequences resemble account takeover. However, traditional warning signs such as failed authentication attempts, unusual login locations or abrupt privilege escalation may not appear. The credentials are valid, the permissions are approved, and the activity remains technically legitimate.
Why monitoring must evolve
Most monitoring frameworks were designed to detect clear signs of compromise: known attack techniques, suspicious authentication attempts or technical anomalies that deviate sharply from expected behavior. That model works well when an attacker needs to force their way in.
Identity misuse follows a different logic. It unfolds within approved authentication flows, recognized infrastructure and valid credentials. Nothing appears technically wrong. The signals are subtle, not dramatic. Instead of triggering obvious alerts, misuse often manifests as small behavioral shifts: access that gradually expands beyond its original purpose, privileges used in new combinations or automated processes interacting with systems in ways that were not initially intended.
Detecting this type of risk requires more than pattern matching. It demands contextual understanding. Security teams must be able to see how identities behave over time and determine whether that behavior still aligns with operational intent. Without continuous visibility into identity activity, these deviations blend into the background noise of normal operations.
Reducing this blind spot goes beyond collecting logs. It requires sustained oversight and informed interpretation. At Cronos Security, identity activity is continuously analyzed within our Managed Detection & Response approach. Authentication events, privilege usage and system interactions are examined in context to identify behavior that drifts away from expected patterns, even when no traditional alert is triggered.
Identity-based threats rarely announce themselves with high-severity warnings. They operate quietly, through legitimate access paths. That is precisely why continuous monitoring and expert analysis are essential. As AI adoption increases and automation becomes further embedded in business processes, identity effectively becomes the control plane of the modern environment. Protecting that control plane means accepting that misuse can look entirely legitimate, until the impact becomes undeniable.